SolarWinds hackers are back with a new mass campaign, Microsoft says

The Kremlin-backed hackers who targeted SolarWinds customers in a supply chain attack have been caught conducting a malicious email campaign that delivered malware-laced links to 150 government agencies, research institutions and other organizations in the US and 23 other countries, Microsoft said.
The hackers, belonging to Russia’s Foreign Intelligence Service, first managed to compromise an account belonging to USAID, a US government agency that administers civilian foreign aid and development assistance. With control of the agency’s account for online marketing company Constant Contact, the hackers had the ability to send emails that appeared to use addresses known to belong to the US agency.
Nobelium goes native
“From there, the actor was able to distribute phishing emails that looked authentic but included a link that, when clicked, inserted a malicious file used to distribute a backdoor we call NativeZone,” Microsoft Vice President of Customer Security and Trust Tom Burt wrote in a post published on Thursday evening. “This backdoor could enable a wide range of activities from stealing data to infecting other computers on a network.”
The campaign was carried out by a group that Microsoft calls Nobelium and is also known as APT29, Cozy Bear, and the Dukes. Security firm Kaspersky has said that malware belonging to the group dates back to 2008, while Symantec has said the hackers have been targeting governments and diplomatic organizations since at least 2010. There’s more about the off-kilter and old-school coding characteristics of this group here.
Last December, Nobelium’s notoriety reached a new high with the discovery the group was behind the devastating breach of SolarWinds, an Austin, Texas, maker of network management tools. After thoroughly compromising SolarWinds’ software development and distribution system, the hackers distributed malicious updates to about 18,000 customers who used the tool, which was called Orion. The hackers then used the updates to compromise nine federal agencies and about 100 private-sector companies, White House officials have said.
Security firm FireEye said that in addition to the USAID content, the hacking group used a variety of other lures, including diplomatic notes and invitations from embassies. It went on to say that the campaign’s targeting of governments, think tanks and related organizations has been a traditional focus for operations conducted by the Foreign Intelligence Service, which is known as the SVR.
“Though the SolarWinds activity was remarkable for its stealth and discipline, loud, broad spearphishing operations were once the calling card of SVR operators who often carried out noisy phishing campaigns,” John Hultquist, Vice President of Analysis at FireEye-owned Mandiant Threat Intelligence, said in an email. “Those operations were often effective, gaining access to major government offices among other targets. And while the spear phishing emails were quickly identified, we expect that any post-compromise actions by these actors would be highly skilled and stealthy.”
Blast from the past
On Tuesday, Nobelium blasted 3,000 different addresses with emails that purported to deliver a special alert from USAID concerning new documents Former President Trump had published about election Fraud. One of the emails looked like this:
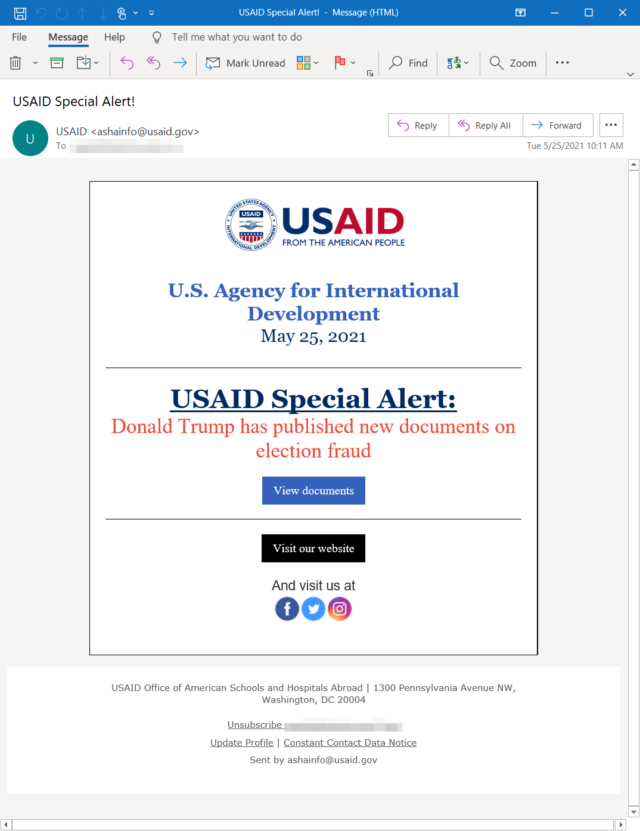
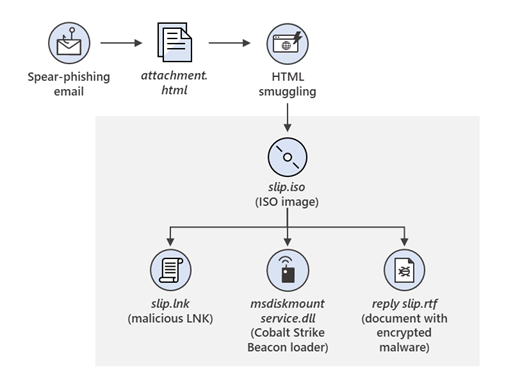
People who clicked on the link were first delivered to the legitimate Constant Contact service, but shortly after that they were redirected to a file hosted on servers belonging to Nobelium, Microsoft said. Once targets were redirected, JavaScript caused visitor devices to automatically download a type of archive file known as an ISO image.
As the image below shows, the ISO image contained a PDF file, a LNK file named Reports, and a DLL file named documents, which by default was hidden.
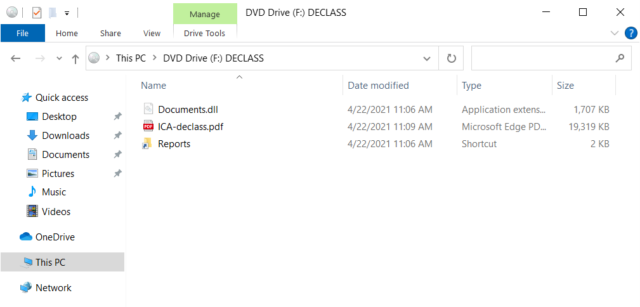
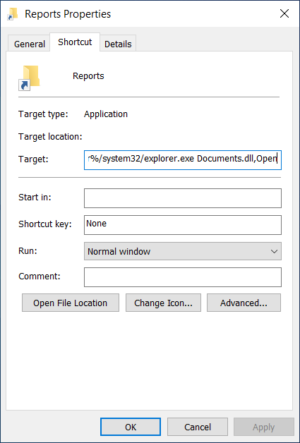
When a target clicked on the Reports file, it opened the PDF as a decoy and in the background executed the DLL file. The DLL, in turn, installed the NativeZone backdoor. A separate post published by the Microsoft Threat Intelligence Center, or MSTIC, said the backdoor allowed Nobelium to achieve persistent access to compromised machines so the group could “conduct action-on objectives, such as lateral movement, data exfiltration, and delivery of additional malware.”
Tuesday’s attack was just the latest wave of what MSTIC said was a widespread malicious spam campaign that started in late January. Since then, the campaign has evolved in a series of iterations that have demonstrated “significant experimentation.”
When Microsoft first saw the campaign, it was hosting the ISO on Firebase, a Google-owned cloud platform for mobile and Web apps. During this early iteration, Microsoft said, the ISO image contained no malicious payload, leading company researchers to conclude the purpose was to “record attributes of those who accessed the URL.” In a later phase, the campaign sent emails that contained an HTML file. When opened, JavaScript wrote an ISO image to disc and encouraged the target to open it.
The flow of this latter attack phase looked like this:
iOS zero-day
Nobelium continued to experiment with multiple variations. In one wave, no ISO payload was delivered at all. Instead, a Nobelium-controlled web server profiled the target device. In the event the targeted device was an iPhone or iPad, a server delivered what was then a zero-day exploit for CVE-2021-1879, an iOS vulnerability that allowed hackers to deliver a universal cross-site scripting attack. Apple patched the zero-day in late March.
Thursday evening’s MSTIC post continued:
Experimentation continued through most of the campaign but began to escalate in April 2021. During the waves in April, the actor abandoned the use of Firebase, and no longer tracked users using a dedicated URL. Their techniques shifted to encode the ISO within the HTML document and have that responsible for storing target host details on a remote server via the use of the api.ipify.org service. The actor sometimes employed checks for specific internal Active Directory domains that would terminate execution of the malicious process if it identified an unintended environment.
In May 2021, the actor changed techniques once more by maintaining the HTML and ISO combination, but dropped a custom .NET first-stage implant, detected as TrojanDownloader:MSIL/BoomBox, that reported host-based reconnaissance data to, and downloaded additional payloads from, the Dropbox cloud storage platform.
On May 25, the NOBELIUM campaign escalated significantly. Using the legitimate mass mailing service Constant Contact, NOBELIUM attempted to target around 3,000 individual accounts across more than 150 organizations. Due to the high-volume campaign, automated systems blocked most of the emails and marked them as spam. However, automated systems might have successfully delivered some of the earlier emails to recipients.
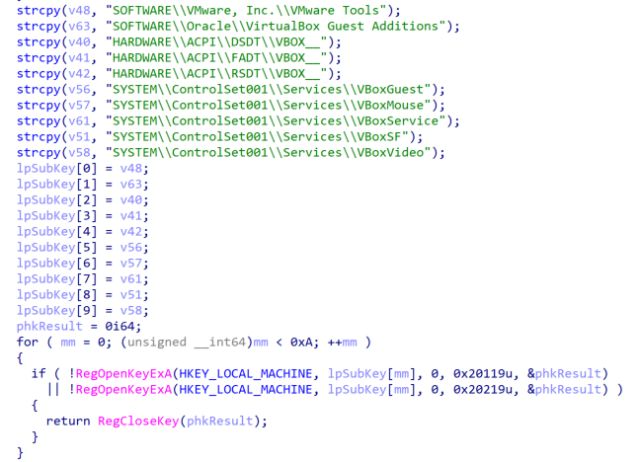
Security firm Volexity, meanwhile, published its own post on Thursday that provides more details still. Among them: the Documents.DLL file checked target machines for the presence of security sandboxes and virtual machines as shown here:
Both MSTC and Volexity provided multiple indicators of compromise that organizations can use to determine if they were targeted in the campaign. MSTC went on to warn that this week’s escalation isn’t likely the last we’ll see of Nobelium or its ongoing email campaign.
“Microsoft security researchers assess that the Nobelium’s spear-phishing operations are recurring and have increased in frequency and scope,” the MSTC post concluded. “It is anticipated that additional activity may be carried out by the group using an evolving set of tactics.”
Post updated at 8:51 California time to add details from FireEye.