Chrome users have faced 3 security concerns over the past 24 hours

Users of Google’s Chrome browser have faced three security concerns over the past 24 hours in the form of a malicious extension with more than 2 million users, a just-fixed zero-day, and new information about how malware can abuse Chrome’s sync feature to bypass firewalls. Let’s discuss them one by one.
First up, the Great Suspender, an extension with more than 2 million downloads from the Chrome Web Store, has been pulled from Google servers and deleted from users’ computers. The extension has been an almost essential tool for users with small amounts of RAM on their devices. Since Chrome tabs are known to consume large amounts of memory, the Great Suspender temporarily suspends tabs that haven’t been opened recently. That allows Chrome to run smoothly on systems with modest resources.
Characteristically terse
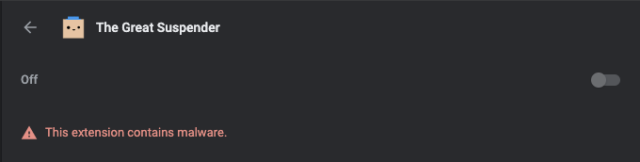
Google’s official reason for the removal is characteristically terse. Messages displayed on devices that had the extension installed say only, “This extension contains malware” along with an indication that it has been removed. A Google spokesman declined to elaborate.
The longer back story is that, as reported in a GitHub thread in November, the original extension developer sold it last June, and it began showing signs of malice under the new ownership. Specifically, the thread said, a new version contained malicious code that tracked users and manipulated Web requests.
The automatic removal has left some users in the lurch because they can no longer easily access suspended tabs. Users in this Reddit thread have devised several ways to recover their tabs.
High severity zero-day
Next, Google on Thursday released a Chrome update that fixes what the company said was a zero-day vulnerability in the browser. Tracked as CVE-2021-21148, the vulnerability stems from a buffer overflow flaw in V8, Google’s open-source JavaScript engine. Google rated the severity as “high.”
Once again, Google provided minimal information about the vulnerability, saying only that the company “is aware of reports that an exploit for CVE-2021-21148 exists in the wild.”
In a post published Friday by security firm Tenable, however, researchers noted that the flaw was reported to Google on January 24, one day before Google’s threat analysis group dropped a bombshell report that hackers sponsored by a nation-state were using a malicious website to infect security researchers with malware. Microsoft issued its own report speculating that the attack was exploiting a Chrome zero-day.
Google has declined to comment on that speculation or provide further details about exploits of CVE-2021-21148.
Sync abuse
Lastly, a security researcher reported on Thursday that hackers were using malware that abused the Chrome sync feature to bypass firewalls so the malware could connect to command and control servers. Sync allows users to share bookmarks, browser tabs, extensions, and passwords across different devices running Chrome.
The attackers used a malicious extension that wasn’t available in the Chrome Web Store. The above link provides a wealth of technical details.
A Google spokesman said that developers won’t be modifying the sync feature because physically local attacks (meaning those that involve an attacker having access to the computer) are explicitly outside of Chrome’s threat model. He included this link, which further explains the reasoning.
None of these concerns mean you should ditch Chrome, or even the sync feature. Still, it’s a good idea to check the version of Chrome installed to ensure it’s the latest, 88.0.4324.150.
The usual advice about browser extensions also applies, which is essentially to install them only when they’re truly useful and after vetting the security in user comments. That advice wouldn’t have saved Great Suspender users, however, which is precisely the problem with extensions.